What is Advanced Persistent Threat (APT)?

Advanced Persistent Threat (APT) is a specialized attack that uses stealth methods to gain unauthorized access to network data. Because of its sophisticated nature of attack, an ATP breach persists quietly until it gets past the security barriers and can stay undetected in the network for a prolonged time.
How Does an Advanced Persistent Threat Breach Enterprise Data?
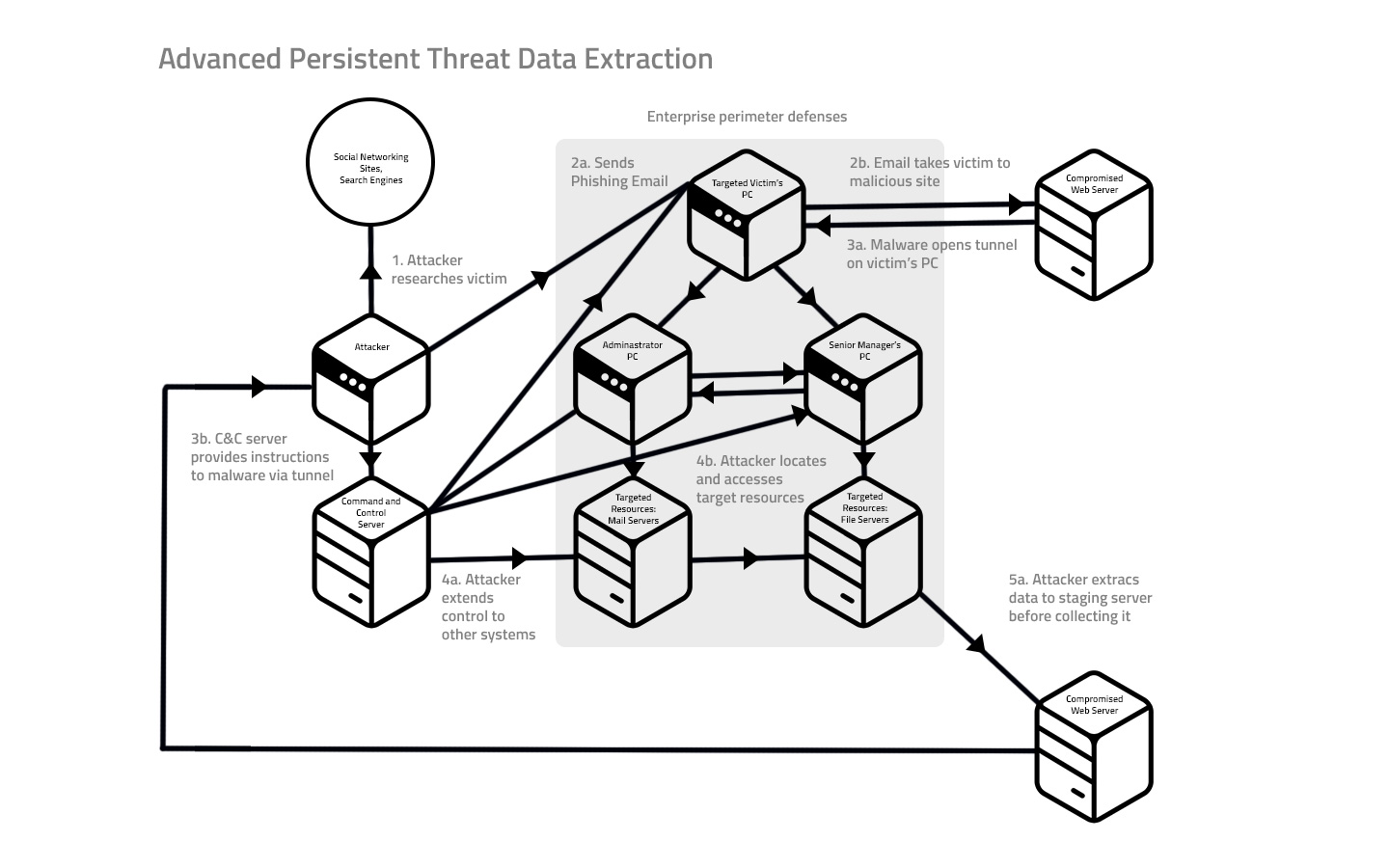
APTs are developed to gain network access with robust evasion system. The attackers make it more complex, and there is a need of a dedicated administrator to check on the intruding malicious activity. APT attackers implement spear phishing, which is an illegal act to send emails through genuine sites. This is done to access the target network and then generates a backdoor to stay connected to the network so as to extract victim's sensitive and confidential information.
Comodo Advanced Threat Prevention
Comodo Advanced Threat Prevention has been developed to defeat Advanced Persistent Threats.. It works at a full measure to fence the network from security data breaches, zero day exploits, known and unknown threats.
The Advanced Threat Prevention operates in integration with Comodo's cloud and internal malware scanning techniques which interrupts automatic file downloads from websites or as email attachments at random. The scan functions to run a behaviour-based and signature-based analysis to deduct the known and unknown threats instantly.
How Does the ATP Work?
The ATP ingrains a holistic approach in securing your network against the APT attacks.
- The cloud-based file look-up service, features to perform a reputation-based security check to validate if the file is genuine by verifying the file's signature against a database of latest threat definitions.
- Comodo antivirus runs automatic updates to index the latest virus definitions and alerts the admins if it identifies known malicious files in your network.
- It performs a real-time audit of all domains, URLs and IP addresses accessed by your network users to see if they are flagged as malicious by blacklisting services.
- Comodo Automated Malware Analysis (CAMAS), a cloud-based behaviour analysis feature, rigorously tests the run-time actions of unknown files and improves detection of zero-day threats.
Comodo Advanced Threat Prevention creates whitelist and blacklist of domains based on risk analysis and offers unparalleled flexibility to network admins who can manually add or remove domains from these lists.
With the help of easy ATP interface, admins can create and manage profiles to be applied for web protection and email protection in Firewall Policy rules, or configure them to license endpoint security software and Comodo Antivirus.
